What we need is first a way to detect these vehicles. However, that’s not enough. We should detect them and then built a publicly available list of all known uses. Its time we get them on a list.
What kind of data does a CSS can collect from a smartphone?
Network traffic
I guess unencrypted internet traffic, right?
Yes, this includes things like phone calls and sms. It also important to note that the FCC could end this practice today.
Interesting, I have noticed CSS positioned in some points of the city always wondered what these was exactly, I thought it was some kind of Wi-Fi spying system but never thought it was radio station spying systems. Interesting.
I’m wondering with the implementation of “AI” to monitor all the communications thought these what LEA could be capable to do.
What you’re noticing are likely small cells, not cell site simulators.
There is no good use for this but repression. If they need to track someone, there are warrants. Cell companies are very willing to comply.
This is crazy and scary. I had no idea a system like that existed.
VPN at all times
A VPN won’t really do anything against CSS/IMSI catchers.
Forgive my ignorance, but isn’t preventing this type of man in the middle attack exactly what VPNs are for?
That’s not how a VPN works. A VPN masks the information you are actually accessing by showing you query the VPN instead. To make a connection to a service you still need an address. This info is what they are using to identify your device.
Most traffic is already encrypted (httpS) so someone spying on you wouldn’t know the content of your communication only who you contact. But without a VPN a man in the Middle could see who you are contacting. E.g. looking up pornhub. With the VPN it only shows you looking up the VPN.
Right, that’s what I understood. So using a VPN, a CSS will be able to identify that my phone is active, but not the content I’m accessing, or who I am accessing it from, correct?
The previous comment said VPNs do nothing against this type of attack- were they just referring to identifying your device?
Right, that’s what I understood. So using a VPN, a CSS will be able to identify that my phone is active, but not the content I’m accessing, or who I am accessing it from, correct?
From my understanding your statement seems correct, but it’s also lacking a bit. Unless you also randomize your mac address (grapheneOS does this) they can still map your position and visiting times. Additionally not all of your phones data goes through the VPN, something like a phone call/SMS isn’t encrypted unless you’re using an app to make the call.
The previous comment said VPNs do nothing against this type of attack- were they just referring to identifying your device?
Yes, they are thinking of a VPN as a privacy tool, not strictly as a security tool as in your example. Privacy will be compromised.
These devices (CSS/Stingray) are going to see both your SIM IMSI number, and your device IMEI number. AFAIK, the MAC randomization that most modern phones do, is with your WiFi modem so that WiFi routers can’t track you.
If you put your SIM card into a new phone, and then login to your cell service provider portal with a computer or other device, you will observe that they know the model of phone you are using. They get this info from the IMEI when your phone talks to the tower. Since the CSS is a rogue tower, they get the same info.
Thanks for clearing up my WiFi mix-up. From my understanding the same attack path still applies even to https://grapheneos.org/features#lte-only-mode and respectively https://grapheneos.org/usage#lte-only-mode correct?
https://en.wikipedia.org/wiki/International_Mobile_Subscriber_Identity states the phone would send a https://en.wikipedia.org/wiki/Mobility_management#TMSI most of the time? But your point about the IMEI still stands. So there is no real way to protect yourself other than to turn off cell tower roaming?
CSS wouldn’t be used to spy on your network traffic; if they wanted your internet data, they’d have much simpler methods to collect it than CSS (and they wouldn’t be able to decode most of that data anyways in normal cases).
or who I am accessing it from
What do you mean by that?
Suggesting that a VPN could mitigate stuff relating to CSS is like wearing a floating vest 24/7 when flying in a Boeing plane: you might feel a bit safer with it on, but it’d probably be smarter to have a parachute instead.
Ok, I’m missing something then.
What is CSS used for?
CSS are used to establish whose phone (the therefore who) is in a location and whose phone (and therefore whomst) sent and received data at what times.
That information is what police will use as probable cause to get warrants against the services you use if not your person or home.
The lower layers all already at least moderately well encrypted, what they’re doing here is trying to pull the unencrypted device ID necessary to establish a connection. It’s not really what you’re sending (though traffic frequency analysis may be included) and more about just figuring out where a particular phone is so they can physically track the user.
Nah, encrypted communication.
This is the one of the few real things that make VPNs a security tool - security from thugs using a MITM attack on your phone. This is also a reason to avoid SMS messaging and port your number to a VoIP service instead of a direct cellular number, as VoIP traffic would be routed over the encrypted VPN tunnel with everything else instead of through the traditional cell network which is vulnerable to these attacks.
If government agents want to know what you’re saying and doing without your consent, you should leave them no choice but to get a warrant and do some actual work.
They’ve had these systems since the 90’s. There’s a documentary about a guy that got caught from one of these its on Netflix. I forget the name. If I remember I will edit this. He went through an insane amount of court documents and files to uncover LE has been illegally using Stingray systems and other custom made devices in cars for decades. They pinpoint physical location down to the square foot.
Edit: Avoid all networks but 5G if possible, use reputable VPN, VOIP. There are apps the send you notifications if your connected to insecure network types one on Fdroid is 5Gcell. The documentary is called Web of make believe: Death, lies, and the internet. Daniel rigmaiden is the guy who exposed the system. Highly recommend if you wanna learn to watch it.
Just here to say thank goodness for the EFF. I support them, and if you live a cushy life like I do and have the money, you should too.
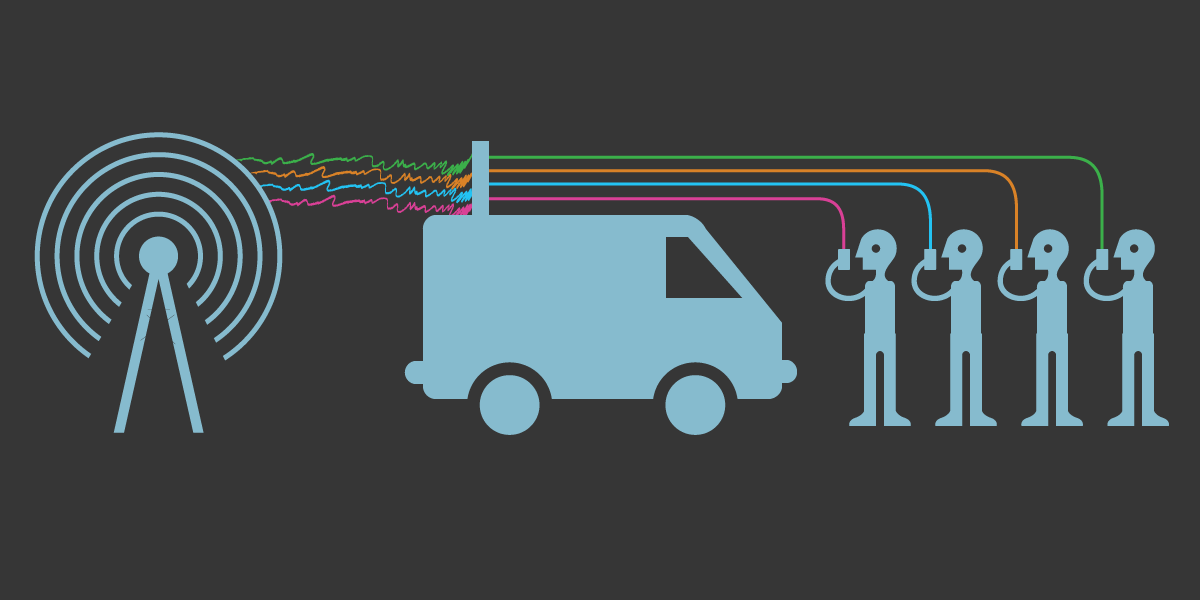
Important to the MSP contract is the modification of a Chevrolet Silverado with the CSS system.

I don’t buy that they don’t have direct access to the cell towers themselves
As far as I understand, RF is RF. All the truck device needs to do is operate on the same RF frequencies as the tower with the correct data form and handshakes (which I’m sure the cell companies happily provide), and boom, you’re connected.
Phones naturally connect to the strongest signal, which will be these things as long as its signal is stronger than the tower, and then the transceiver on the truck connects to the cell tower and is configured to MITM snoop as traffic is passed through the truck device on to the tower and vice versa.
No, I mean, I’m saying I doubt they even really need the trucks, except maybe as an explanation of how they got the data legally.
I think the whole point is location tracking and identification. You figure if they want to go after a group of protestors, all they do is set up their tig near them and they’ll instantly have every device in the immediate area that they can chase down. And let’s be real here, they don’t give two fucks about legality anymore, they’re in full suppression mode. All the more reason to never bring a phone to a protest in the US.
If there are two or more cell towers within range of the phone and they have access to those towers they can triangulate the location of the phone already.
deleted by creator